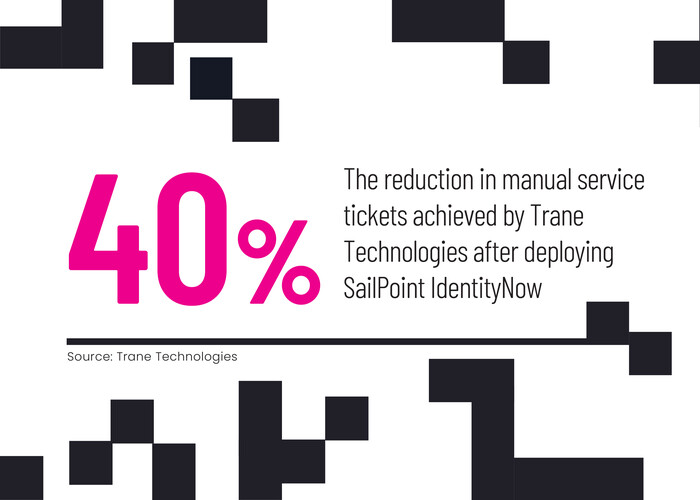
When Trane Technologies’ technicians are in the field, they need instant access to their IT applications to serve the company’s heating, ventilation and air conditioning customers. At the same time, the Davidson, N.C.-based company’s IT staffers must support a sophisticated technology ecosystem, and constant tickets for manual additions, changes and password resets were proving to be a distraction.
For Trane Technologies, the solution to both challenges lay in one tool: SailPoint’s IdentityNow.
“We were getting 100,000 tickets per year related to identity management,” says Aaron Havenar, senior IT security analyst at Trane Technologies. “Each ticket took around 45 seconds, but we were doing it so often, and it was becoming more frequent as the company grew. It became unsustainable for our lean IT group.”
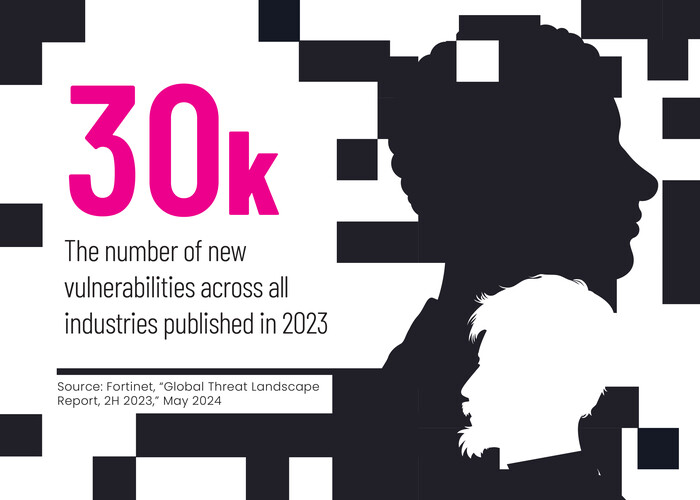
This challenge is increasingly common as IT systems grow more complex. Modern identity and access management tools emphasize continuous authentication, least privilege access and dynamic risk assessment models that leverage artificial intelligence.
“Effective IAM provides organizations with visibility into who is accessing systems and data, fortifies zero-trust architecture principles, and ensures compliance with regulatory requirements,” says Sakshi Grover, senior research manager for cybersecurity services at IDC.
Click the banner below to learn why cyber resilience is essential to enterprise success.

Obsolete IAM Solutions Are Clunky and Error-Prone
The manual identity management processes previously used by Trane Technologies were labor-intensive and error-prone. “A finger in the wrong spot on the keyboard might create a misspelling that we would then have to go back and change,” Havenar says. “We were constantly creating network accounts for new users and then making updates. If someone’s last name changed, or if they moved locations, that would be another ticket.”
By integrating with authoritative internal data sources, such as the HR system, SailPoint’s IdentityNow solution can make instant, automated updates to the company’s Active Directory environment. After adopting SailPoint, the company was able to get new employees set up on their first day of work rather than sometime during their first week, Havenar says. That means that new employees and contractors are no longer sitting idle, waiting to access the tools they need for their jobs.
When Trane Technologies first implemented IdentityNow, the tool found several former employee accounts that still had access to legacy applications. While these accounts could not see sensitive data, Havenar says, it was still important to find and delete them to ensure that only authorized users can access company systems.
“Identity management has rapidly changed over the past two or three years,” Havenar says. “We have employees, we have nonemployees, we have contingent labor. And then we have nonhuman entities, things like cloud accounts and API credentials. The space has grown, and we need to keep up as best we can. SailPoint is doing a great job giving us the capabilities we need to do that.”
Back to the article
Autoplay
Full Screen
Grid View
Exit Full Screen
Back to the article
Autoplay
Full Screen
Grid View
Exit Full Screen
How To Automate Identity Management
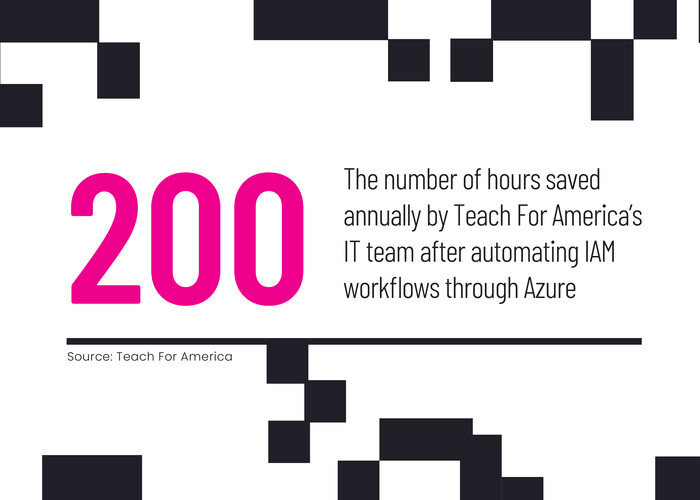
Teach For America, a nonprofit that finds, develops and supports educational leaders, recently centralized its IAM environment on Microsoft Azure, using Microsoft Entra ID (formerly Azure Active Directory) B2B and B2C to manage the identities of full-time staff and teaching corps members and of external users, respectively.
“Identity is the foundational keystone as we transform into becoming a digital-first program,” says Alan Murray, Teach For America’s chief digital digital & technology officer. “They get automatically the things they need access to through OneApp, our new digital experience. The overhead is much, much lower. We don’t have as many operational tasks to scramble to do and deal with all day long.”
The use of Microsoft Authenticator, gives the organization access to what Murray calls “true” multifactor authentication. “Before, we had a secondary challenge question for logins, but that’s not really MFA,” he says. “The questions and answers never changed, and it wasn’t where it needed to be for security and risk management.”
Looking ahead, Murray expects his team to further automate identity management through Azure’s capabilities. This will lighten the management load for IT staffers and improve the user experience for staff and corps members. “We’re getting tremendous scale now that doesn’t rely on people taking manual actions,” he says. “Our staff doesn’t have to lift a finger, and users get access to what they need instantly.”
IAM Isn’t Just for Internal Users
Rotary International needs to make its IT systems available to more than just its nearly 1,000 employees. The global service organization has 1.2 million members spread across 45,000 clubs around the world. The leadership at each of these chapters turns over every year, creating additional hurdles to providing role-based access.
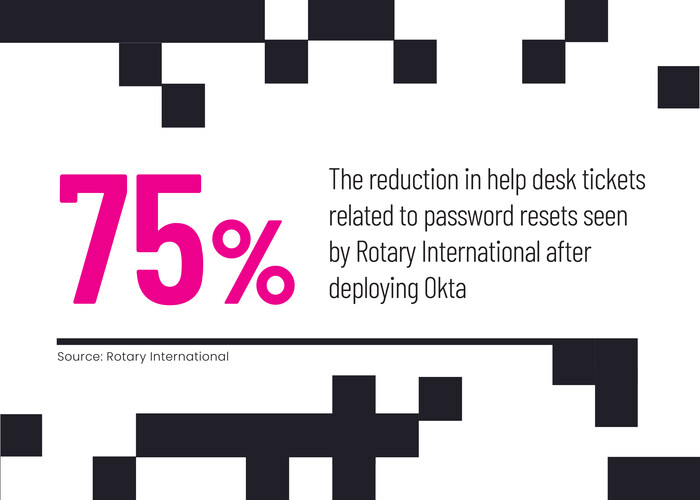
It’s a challenge that can only be solved with sophisticated IAM tools that automate the provisioning of role-based access while providing scalable authentication and seamless integration with solutions such as customer relationship management systems. Rotary employs Okta, a cloud-based IAM platform that enables single sign-on for its internal and external applications and protects sensitive data for its high-profile members, youth program participants and others.
“Our members use Okta to access our member portal, MyRotary,” notes Cris Downey, director of technology services and information security. “They can manage their personal information, make donations, and access the applications and services that we make available to our members, such as online courses in leadership.”
Click the banner below to learn why identity access solutions can help your organization.

The instant scalability of a cloud solution such as Okta, Downey says, means that Rotary can instantly provide authentication management for new users, and the organization doesn’t see performance degradation when a large number of members are using the system at once. The tool has been particularly effective at warding off distributed denial-of-service attacks and other hacking attempts against the organization’s VPN.
“We see tens of thousands of attempts, but malicious actors can’t get inside,” Downey says. “Attackers can’t get around the multifactor.”
Next, Rotary intends to simplify its IAM processes, perhaps allowing users to access resources using their Google or Apple credentials in a federated login system.
At the organization’s annual convention, members can register for the following year’s event via onsite kiosks, and Downey will sometimes ask people in line if they remember their usernames and passwords. Invariably, he says, they look back at him with a “blank stare.”
“Using a standardized but secure access method, where people don’t even need to remember a password, that’s the next key step,” Downey says. “We want to simplify access as much as possible while still being as secure as we can.”
Getty Images: A-Digit, bgblue, A Mokhtari, Elena Bereberdina