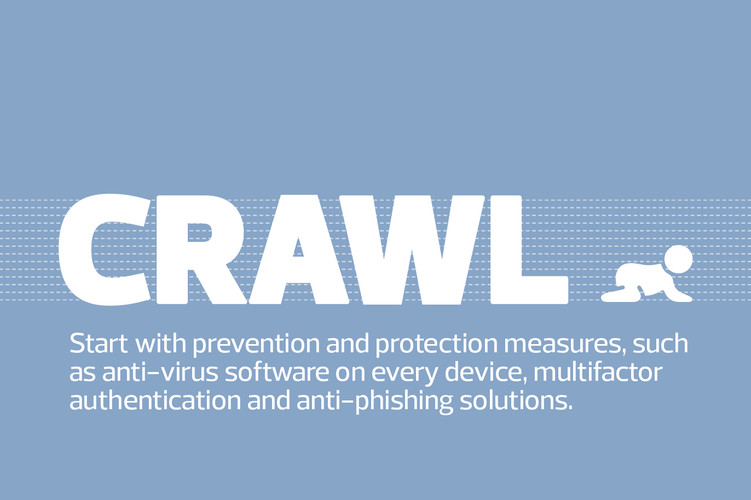
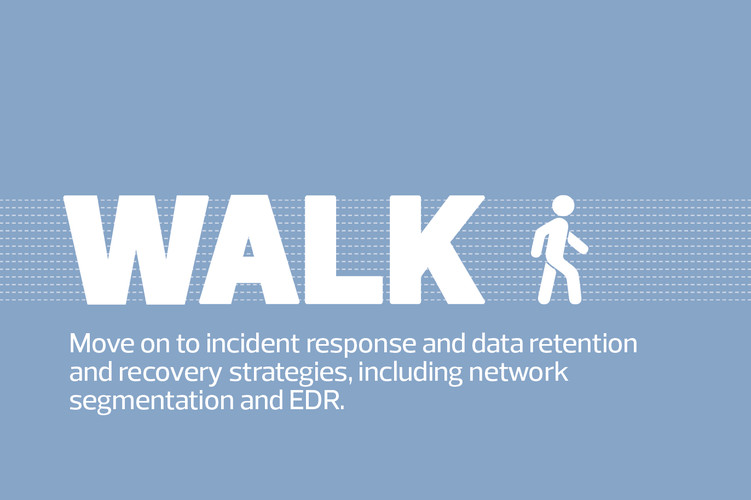
Record-setting cyberattacks prompted SonicWall to declare 2021 “the year of ransomware,” and the threats haven’t abated. But as attackers have matured, so have their targets. Businesses are upping their security defenses, beginning with basic prevention and building toward artificial intelligence tools and a zero-trust posture.
What’s fueling the urgency is that ransomware has itself become a thriving industry, particularly in the age of cryptocurrency, which makes it easier for attackers to get paid. Anyone can purchase Ransomware as a Service on the dark web.
“It’s a business at this point,” says Candy Alexander, board president of ISSA International. “The malicious threat actors are going to continue to grow their business because it works. It’s very entrepreneurial, in a bad way.”
Alexander urges businesses not to pay ransoms unless it’s a life-or-death situation, because payouts buttress the ransomware industry. If no one paid, it would collapse. Either way, she adds, businesses should determine before they get hit whether they would pay a ransom or try to recover and rebuild.
The risks can’t be ignored, Jauregui says: “It’s probably weird for this field, but I’m kind of a low-key person. Still, there are things that occur in this job that can raise the hairs on the back of your neck. Having something like Falcon Complete helps a laid-back person like me remain calm during taxing times.”
DIVE DEEPER: Learn how cybersecurity needs have changed in recent years.
A Robust Security Strategy Requires a Layered Defense
At LEO A DALY, an Omaha, Neb.-based architecture, planning, engineering and interior design firm, all it took was one person in accounting clicking on an email link. The ransomware spread to the employee’s contacts, including someone with administrative privileges, and to all the network drives across the firm’s 30 offices.
IT shut down external communication to the server, then worked with the company’s cloud storage vendor, Nasuni, to clean up the ransomware and determine what hit it. With help from Microsoft, they determined that it was the Trojan:Win32/Zlader threat, got the decryption key, then restored the network from the company’s Nasuni immutable storage. That was in 2016.
Looking back, CIO Stephen Held says, the attack prompted the firm to add cybersecurity protections to prevent future attacks. For instance, back then, the firm didn’t have a good method for recalling ransomware messages from employees’ emails, so others fell for the same attack over the following days. Now, IT staffers recall messages regularly. They’ve also locked down administrative privileges.
Before the 2016 attack, LEO A DALY hadn’t done much to train users to recognize and report phishing emails, but the company now uses KnowBe4 for training and phishing simulation.
It has also implemented Arctic Wolf’s hosted security incident and event management service, which provides active monitoring and alerting for workstations and servers, Held says: “They have the ability to shut it down before it propagates.”