Phishing Is a Stubborn Problem
Phishing attacks have been around for years, but they continue to hook employees for a variety of reasons, says Joseph Blankenship, vice president and research director for security and risk at Forrester Research.
“If you catch someone with the right message, or at the wrong time, or if they’re distracted, that has a role to play,” Blankenship says. “This is a very human problem. It’s not entirely a technology problem, and it’s not a user problem. It’s about giving the users enough training and awareness so they know what to do when they face the situation.”
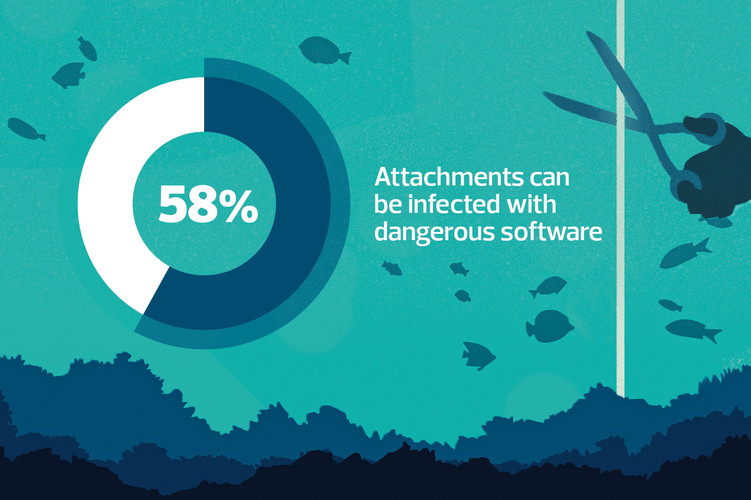
The FBI’s Internet Crime Complaint Center received more than 240,000 phishing complaints in 2020, with losses totaling more than $54 million. Blankenship says that according to a 2019 Forrester global survey of security decision-makers, phishing attacks were involved in 23 percent of external data breaches.
The Forrester report outlines a representative phishing instance: A scammer, spoofing a CEO’s email address, asks a low-level employee to run an errand. Then, after the worker replies, the scammer clarifies that the employee needs to buy gift cards for a customer recognition program, using a company credit card or petty cash. By the time the “CEO” asks the employee to send photographs of the card activation codes, the employee’s guard is already down, and he or she may not even think to question the request.
The Forrester report recommends several tools and best practices, including email content filtering and authentication, threat intelligence, and security awareness training. Blankenship adds that any phishing simulations should mirror real-world scenarios as much as possible.
“When you do a simulation, you should do it in a way that takes into account the way that the firm is currently being targeted, using threat intelligence or relying on a vendor to let you know about changing approaches,” he says. “You want to get real-time feedback and then use the reporting to gauge risk and improve over time.”