For all the talk of insider threats — a very real problem — the truth is most attacks, including ransomware, come from outside an organization’s network. For example, 70 percent of breaches in 2020 were caused by outsiders, according to Verizon. Meanwhile, IBM pins the most common cause of breaches in 2021 on stolen user credentials.
It’s clear that while good security policy and well-trained staff are important to keeping businesses safe, investing in the right protection is also vital.
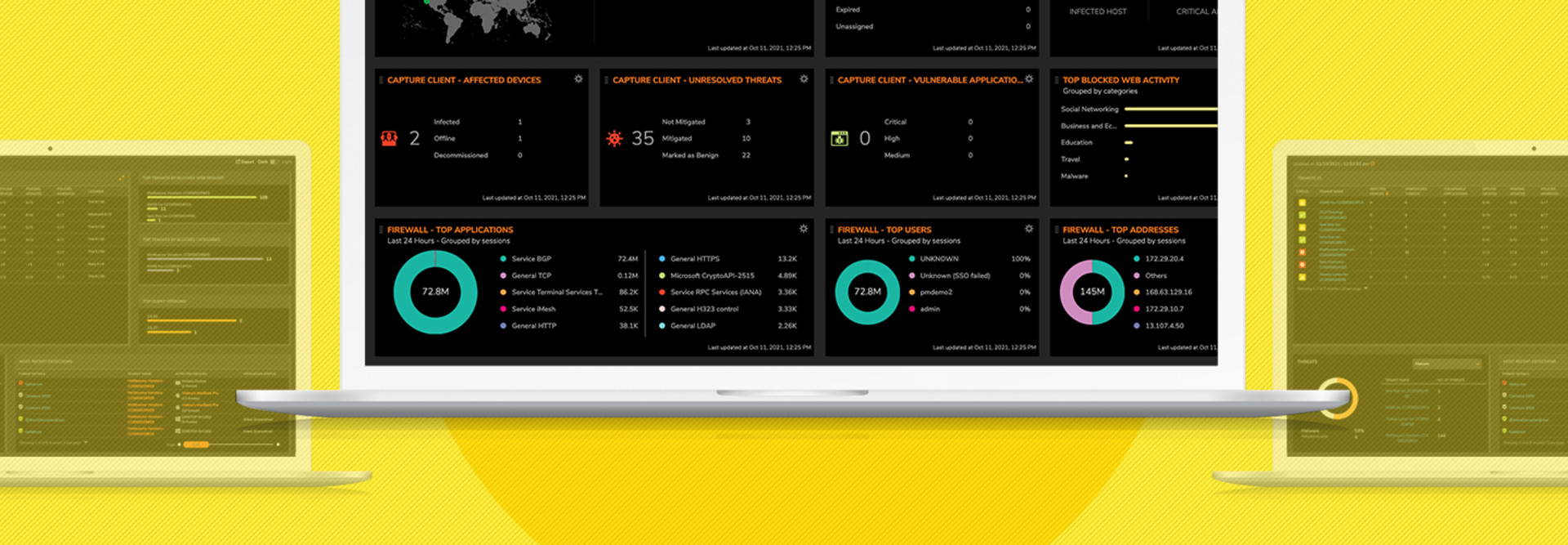
My recent test of SonicWall’s advanced endpoint protection solution left me impressed with its ability to provide continuous behavioral monitoring, easy threat hunting, and a multilayered heuristic approach to determining potential network anomalies. It all combines to produce highly accurate determinations of active threats with very little noise or false positives.
Save Time While Defending Your Environment
SonicWall Capture Client makes it easy and intuitive to create rules that allow or block various activities and alerts. This lets the platform take automatic actions, buying human defenders time to examine and respond to ongoing threats. Other helpful tools include automated malware analysis and built-in advanced threat protection.
Click the banner below to unlock exclusive security content when you register as an Insider.
From a single interface, administrators can see which devices are online and operating and check their security status. Policies can be assigned to entire groups, types of devices, the whole network or even individual endpoints. The platform can even monitor encrypted HTTPS and other SSL traffic.
When a threat is detected, SonicWall Capture Client makes it easy to understand the nature and scope of the problem. It also simplifies the process of capturing threat intelligence and sharing it among team members or as required for regulatory compliance.
Insider Threats Foiled by Capture Client
While outside threats are the top vulnerability organizations face and thwarting them is SonicWall Capture Client’s greatest strength, it doesn’t shrink from tackling the risks posed by malicious insider activities. This includes blocking threats delivered through USB devices inserted into endpoints.
The SonicWall cloud-based management console also lets IT security administrators monitor and evaluate the health of each tenant by showing the number of infections and existing vulnerabilities. This visibility management program also identifies what and who is being blocked.
Meanwhile, Capture Client’s next-generation malware protection engine, powered by SentinelOne, includes machine learning to keep up with changing threats and a multiengine sandbox to isolate anomalies, and can perform a full system rollback with a single click.
Putting so many advanced features into an easy-to-use interface makes the SonicWall Capture Client an excellent choice for protecting modern businesses with large networks and many public-facing assets.
Top Security Features of Cyber Compliance
Businesses of all sizes struggle with regulatory compliance, and in certain industries, such as healthcare and financial services, the requirements are rigorous. SonicWall Capture Client can help. The solution offers security policy enforcement and allows administrators to see all application vulnerabilities. That’s a huge timesaver for IT teams trying to prepare for audits.
Additionally, single-click rollback capabilities give organizations a powerful tool in restoring services and maintaining compliance. SonicWall’s ability to quickly create global policies makes it easy to establish or update compliance and regulatory requirements. The platform can also enforce content-filtering policy issues.
Capture Client allows administrators to apply a single baseline policy to all tenants, which makes it much easier to create new ones, while also enabling administrators to quickly view the global health of all tenants.
Finally, when the Capture Client “inheritance” option is activated, all new tenants acquire existing account policies as soon as they come online. Even so, unique policies can still be created and modified for individual tenants, covering everything from content filtering and malware protection to DPI-SSL certificate management.
Specifications
LICENSE TYPE: Subscription
LICENSE QUANTITY: One endpoint
VALIDATION PERIOD: One year
OS COMPATIBILITY: macOS, Windows