Security Assessments Prove Crucial in Fight Against Hackers
In the past two years, the Cantor Colburn law firm has noticed a shift in clients’ expectations when it comes to data security.
There have always been a few companies that submitted cybersecurity questionnaires before engaging the firm, but it’s now standard practice for most prospective clients of the Hartford, Conn.-based patent and intellectual property firm.
“Nearly every request for proposal now comes in with that,” says Dave Christensen, a Cantor Colburn partner. “Companies have become increasingly aware that their outside vendors are potential weak links, so they’re trying to close that gap.”
Security Is a Modern Business Imperative
Intellectual property is at the core of its business, so Cantor Colburn has always invested heavily in cybersecurity. To put more weight behind assurances that its systems are secure, the firm hired an independent third party, CDW, to validate its infrastructure.
“Even if you have information security staff, I don’t think you’d have the breadth of knowledge that you get by engaging a group that does this day to day,” says Joel Lepage, the firm’s IT director. “I can’t stress enough how valuable this was for us.”
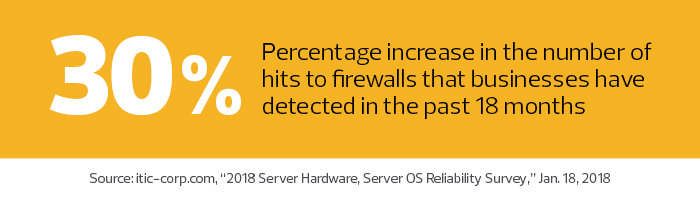
Security assessments make sense for all organizations, but especially for small and medium-sized businesses, says Laura DiDio, principal analyst for research firm ITIC. Applications have become increasingly complex, and the growing number of devices on networks creates unprecedented threat levels.
“If you are an SMB, what is the likelihood that you have a security guru who gets trained regularly on new threats?” DiDio asks. “It’s like having a one-armed outfielder, and it’s raining fly balls. It pays to say, ‘We need more eyes on this.’”
Cybersecurity Assessments Take Many Forms
Cantor Colburn underwent a gap analysis — extensive interviews to review a company’s security controls — as well as internal, external and wireless penetration tests, in which a white hat hacker attempts to infiltrate the company’s network.
Other types of assessments include red teaming, in which testers attempt to access the network undetected; purple teaming, which pairs assessors with clients during an attack to review logs and discuss defense strategies; application vulnerability testing, which looks for holes in web applications; phishing, which tries to deceive employees via email or phone to gain access to the network; and physical social engineering, in which in-person testers try to dupe their way into restricted buildings or areas.
Security assessments often uncover issues that companies don’t know to look for, such as unsecured digital signage or printers, explains Mark Lachniet, manager of CDW’s information security solutions practice. Other times, Lachniet said, it’s not the configuration that’s flawed; it’s the system itself.
“Everybody needs to know what their weaknesses are,” Lachniet says. “Having someone look at things who takes an attacker’s viewpoint is the preferred way to find them.”
Ian Odette, CDW security consulting engineer, spent one week gathering online information about Cantor Colburn for the external penetration test. Odette then spent the following week at the firm’s headquarters, where he attempted to hack the network from the inside.
“Our goal is to get them as exhaustive a list as possible of serious threats, with recommendations for remedying them,” he explains.
During the internal test, Odette used Microsoft’s Group Policy to gain access to secured resources on the network. Cantor Colburn had already implemented Group Policy according to Microsoft standards, but it was a newer exploit that the firm had not yet discovered.
“He showed us how he got in, told us what we can do to fix it, and we were able to address it immediately,” Lepage says. “It was an easy, no-cost solution to tighten our security significantly.”
Security Assessments Are a Year-Long Process
James Foster, CDW information security consulting technical lead, conducted a gap analysis based on the National Institute of Standards and Technology’s Cybersecurity Framework. He gathered information about the firm by phone, then spent three days interviewing IT staff and business unit managers to learn about Cantor Colburn’s mission, its regulatory requirements, how it provisions users, the technology it uses to prevent or detect attacks and more.
“The interview process with CDW was enlightening and enjoyable because they are true experts in the field,” says Lepage. “We learned quite a bit. We were able to bounce ideas off of them, and there was zero condescension.”
The gap analysis uncovered several beneficial policy updates.
One was to formalize Cantor Colburn’s business continuity plan. The firm has grown from a single office in Hartford, which doesn’t experience many extreme weather emergencies, to additional offices in Troy, Mich.; Alexandria, Va.; Atlanta; and Houston, where threats of hurricanes, flooding and tornadoes are present.
“It wasn’t just about security,” says Christensen of the gap analysis. “I was able to ask them about other things related to IT, and given their breadth of experience, it was nice to get affirmations or suggestions on what
we could improve.”
An assessment can build a company’s security posture, but preparing for one is valuable in itself, says John Firman, CTO at Qualpay, a payment processing firm. “The process opened my eyes to various things that I wouldn’t necessarily have thought about,” he says.
Since its launch in 2014, Qualpay has commissioned annual assessments to comply with the Payment Card Industry Data Security Standard, but it chooses to go beyond those requirements.
It conducts full penetration tests twice a year and undergoes monthly vulnerability scanning, a comprehensive probe of a network that detects and classifies weak points.
Each year, teams from Qualpay’s qualified security assessor spend a week in its San Mateo, Calif., headquarters and a day in its Spokane, Wash., operations center performing deep dives into their security procedures.
“It’s that week of onsite where the rubber hits the road, but it’s a year-round process,” Firman says. “There are tasks that we do quarterly and monthly and sometimes even weekly related to security and compliance. It forces you to be constantly checking to make sure you’re still secure.”
To prepare for the annual assessment, Firman and Todd Troutman, Qualpay’s senior systems administrator, review up to 40 security policies to ensure each is up to date. They also check for proper systems documentation, such as network and data flow diagrams.
Among the most valuable security policies for any business are using
two-factor authentication, properly configured email systems so the corporate domain can’t be spoofed, and a centralized network management interface that can spot anomalies and send alerts.
Businesses of All Sizes Need Security
No business is too small to benefit from an independent security assessment.
In 2014, Rich Wooldredge and Jody Hartle turned their side job selling produce, honeybees and free-range chickens at farmers markets into a full-time operation.
They rented a small Elkin, N.C., building and began selling premade meals and other food products derived from their family farm at Barking Coyote Farm Store and Cookery.
Wooldredge wanted to ensure they weren’t jeopardizing customers’ financial data, so he hired a local company to conduct a risk assessment — something the pair would like to do again as they prepare to move to a much larger space, where they’ll have dedicated internet service with separate secure networks for employees and guests.
“If people trust us with their information and we don’t handle it right, I wouldn’t blame them if they didn’t do business with us anymore,” Wooldredge says. “An outside entity with the expertise and knowledge can point out things that you may not have considered.”
That detailed intelligence is exactly what Cantor Colburn received. The analysts conducting its assessments gave the firm detailed lists of suggestions ranked by greatest benefit/lowest cost. That helped the firm prioritize projects, says Christensen.
Cantor Colburn didn’t have to purchase any new systems after the assessment. All improvements involved modifying or updating their existing systems and processes.
“There was almost no impact from a budget perspective,” says Lepage.










