4 Best Practices for Backing Up Endpoints in Your Business
The risk of data loss can keep any IT manager up at night. Disappearing data can cause major expense and even serious damage to the credibility of a business and significantly affect the productivity of individual employees and workgroups.
Endpoints are particularly vulnerable, with risks springing up like a perpetual game of Whac-A-Mole: user error; unauthorized data modification or other malicious action; and mobile devices being damaged, lost or stolen.
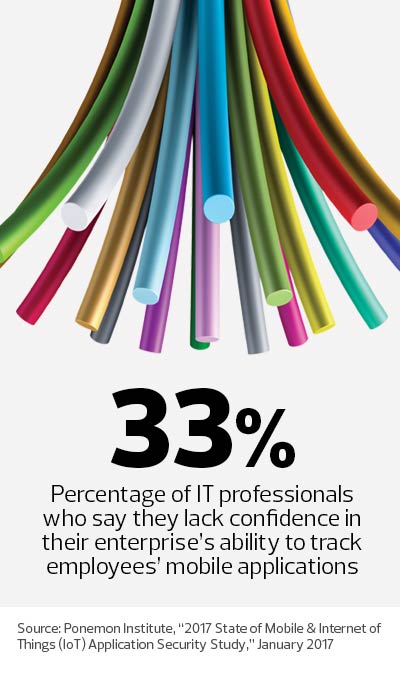
Today’s vast number of mobile workers and the adoption of BYOD programs add to the challenge. Critical and even sensitive data roams out and about on endpoints not always under the direct control of a company’s IT team.
Although backups might simply involve regularly copying files to a USB drive or cloud-sharing service, the most effective strategies encompass far more. It’s important to start with up-to-date operating policies, and then assure the integrity and security of data on all authorized devices.
Best practices and solutions will make these backups simpler, certain, compliant and complete.
To do that requires incorporating these tactics to help lock down endpoint security:
1. Make Backups Automatic and Easy for Users
End users must comply with company-specific backup requirements but should not be responsible for implementing them.
Although it is acceptable for users to make working copies with a flash drive or online (if secure and within policy), the company should require employees to regularly connect to the corporate network for backups.
Backup solutions should be automatic and transparent at best, and at the very least easy — ideally with no user interaction required. The IT team should train users about how to restore information, unless IT handles this function on behalf of users.
 2. Cloud Backups Keep Data Safe
2. Cloud Backups Keep Data Safe
It’s easy today to use public and private clouds for backup, with a wide variety of cost-effective products and services available.
The cloud also has a huge advantage over local backup volumes: The technology minimizes losses that can occur because of events such as fire, flood, theft and related physical security issues. It may also be desirable in some cases to use two backup solutions simultaneously for both local and cloud storage — the suspenders-and-a-belt approach.
3. Mobile Device Management Protects Corporate Data
Use mobile device management and mobile content management solutions.
Backup is integrated into most MDM tools, and MCM uses software containers to isolate corporate data, which a company can back up and manage separately from user data. This is the preferred BYOD strategy; the IT department is not responsible for noncorporate data.
4. Make Your Backups Comprehensive
Backups should be just as secure as any other data. This means that backup data encryption, authentication (ideally two-factor) and authorization must comply with security policy.
To maintain integrity, preserve multiple generations and copies. Also, check whether any industry-specific regulations require additional measures.
Some might argue that damage to data is so uncommon now that anything beyond infrequent backups is unnecessary. But the potential for loss of productivity is real. By applying a few simple, cost-effective techniques, a company can go a long way toward assuring continuity when a backup copy is required, as well as supporting data loss prevention and disaster recovery.