The 3 Main Ways Ransomware Spreads in 2017
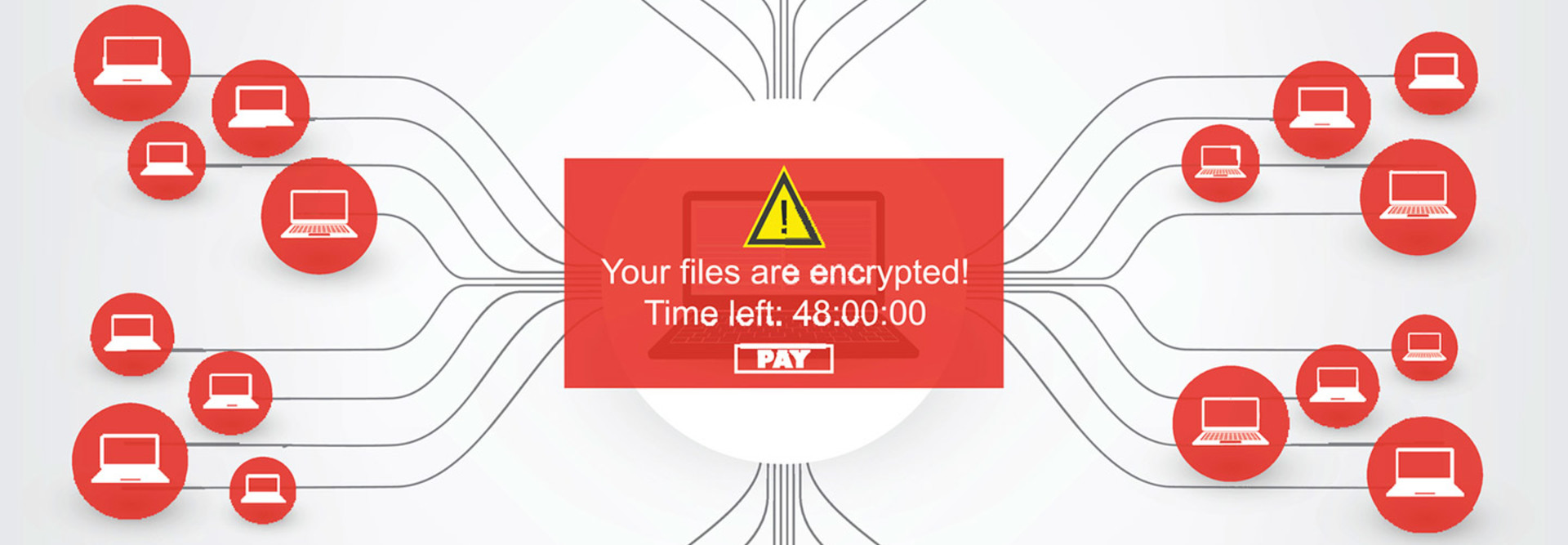
Ransomware is now on everyone’s mind, thanks to the recent “Petya” or ”Nyetya” global malware attack and the earlier WannaCry attack. Ransomware — malware designed to encrypt files and only decrypt them if the victim pays a ransom, usually in the digital currency bitcoin — is being spread in numerous ways, some of which are hard to defend against.
Dan Siebert, an inside sales engineer for security at CDW, noted during a recent CDW webinar sponsored by Trend Micro that ransomware attackers will use a variety of evasion tactics to avoid getting caught and keep attacks going.
SIGN UP: Get more news from the BizTech newsletter in your inbox every two weeks!
1. Traditional Email Is Still an Easy Route In
For example, attackers might use the Tor protocol to conceal their location. Or they might use fast flux, a Domain Name System (DNS) technique used by botnets to hide phishing and malware. Sometimes attackers can engage in “domain shadowing” and create a fake website within a legitimate website that redirects users to a site that launches malware. Or they can lure users to a fake site masquerading as a real one.
Attacks can last for two or three days or a week, Siebert said, and the attackers need to keep moving to different IP addresses and locations. Often, he said, they will use a domain-generating algorithm — an equation that will spit back new domains to the attackers after pinging DNS servers. Some services like Cisco Umbrella can protect users from these tactics, but attackers generally “know how to keep moving their infrastructure” to keep attacks going.
SIGN UP: Get more news from the BizTech newsletter in your inbox every two weeks!
However, Siebert said, 60 percent of ransomware is still distributed via an email, usually through a bad file, a Microsoft Word document or a .ZIP file. Siebert noted that Cisco Systems’ 2017 Annual Cybersecurity Report found that 65 percent of email traffic is spam, and that about 8 to 10 percent of the global spam observed in 2016 could be classified as malicious, which would add up to at least a billion malicious emails, Siebert said. Even if email filters flag the traffic as malicious spam, attackers can usually get hundreds of thousands of messages out within minutes.
“Your coworkers, at the end of the day, we’re going to put all of these IT systems in place, and they are going to be the weakest link,” he said. “Because the individual at the other end, it’s not a computer that is generating these emails. It’s an actual person who speaks English, who knows IT, who knows the infrastructure and stuff you are putting in place. They are crafting this message, they are crafting these files to play on the nature of the person who is receiving that email.”
2. Malvertising Stealthily Spreads Ransomware
A year ago, Siebert said, email accounted for 70 to 75 percent of ransomware transmissions. Increasingly, “malvertising,” or malware hidden in online ads, is being used to spread ransomware, he noted.
Attackers pay for legitimate ads, which, when clicked, redirect users to an exploit server, which then redirects them to a gate server. Attackers will then be able to determine the victim’s operating system, browser and plug-in status. Using that information, they can then determine the best vulnerabilities to exploit and the best kind of malware to run.
“A lot of these attacks are going to start moving more toward that malvertising, and it’s hard for a customer, it’s hard for us as an IT group to block all of those sites out,” Siebert said. Google blocked 780 million bad ads in 2015 and 1.7 billion in 2016, but Siebert said that until online advertising networks do more to block malicious ads, the problem will persist.
3. Ransomware as a Service Makes It Simple
Ransomware as a Service, in which attackers pay for exploit kits like Angler, Nuclear and Neutrino, allows hackers to easily target a victim’s vulnerabilities and run ransomware, Siebert noted.
They then pay a kickback to the designer of the kit, usually 10 to 20 percent of their total ransom haul.
“So, you have the bad guys who are programming the architecture and the infrastructure on the back end, and you have other guys who just want to run a campaign,” he said.
For more information, check out, "What Is the State of Ransomware in 2017?" And for more on the evolving threat of ransomware, the damage these threats can cause and how you can stop them, check out this CDW webinar sponsored by Trend Micro.