How Banks Can Find the Right IT Tools to Comply with Regulations
As the senior technology officer at Premier Financial Bancorp Inc., Greg Napier always has someone looking over his shoulder.
“We have an extremely significant compliance and reporting burden,” Napier says. State and federal auditors, along with the company’s senior managers, want proof that the bank remains in compliance with the myriad privacy and data security regulations that govern financial institutions.
“Being a bank, we are monitored by multiple agencies, starting with the Federal Reserve, the Federal Deposit Insurance Corp. and the West Virginia Department of Finance,” he says. “And they all have specific, often different, requirements.”
In addition to 24 locations in West Virginia, home of its corporate headquarters, Premier Financial also has branches in Kentucky, Ohio, Maryland, Virginia and the District of Columbia. The scrutiny of regulators has grown with the company, Napier says. To keep up with compliance demands, the bank contracts with an outside auditing firm to review procedures, policies and controls. Having also outgrown the software it had used for patch management and tracking, the company recently moved to IBM BigFix Patch.
“Once we became a billion-dollar enterprise, the examiners from the FDIC and others started to look at us differently,” Napier says. “They put a lot more scrutiny on things like patch management.”
SIGN UP: Get more news from the BizTech newsletter in your inbox every two weeks!
Tech Can Automate Compliance Processes
While financial institutions have felt the squeeze of increased compliance and reporting requirements longer than companies in other sectors, regulatory pressures have grown for all industries, says Angela Gelnaw, a senior research analyst at IDC. More companies now look for technologies that automate compliance processes to help relieve that pressure, she says.
To select the right compliance tools, an organization should first consider its infrastructure, budget and the technical skills of its staff, and should also assess whether it has developed processes that are easily automated. “Expecting the tool to fix your processes will lead to big problems,” Gelnaw says.
After that assessment, company officials can assemble a list of features to meet their needs. Included among them should be policy automation, centralized risk registers and analytics, Gelnaw says. Timely reporting that’s both customizable and includes out-of-the-box support for major compliance frameworks — such as the Sarbanes-Oxley and Gramm-Leach-Bliley acts and the Payment Card Industry Data Security Standard — is necessary to satisfy both examiners and C-level management, she says.
Once an organization has a features list, it’s time to research products and directly engage with manufacturers, says Raef Meeuwisse, director of cybersecurity and data privacy governance for consulting firm Cyber Simplicity. He advises sharing the list with vendors to see if they can suggest additional features or requirements and then asking them how their products match up to the list. Additionally, request case studies and customer references, and ask hard questions about implementation and performance.
“To be beneficial to an organization, any compliance technology must be easy to set up, quick to deliver value and straightforward to integrate with wider compliance efforts,” Meeuwisse says.
Build a Relationship with Technology Partners
At Premier Financial, deployment of IBM BigFix Patch went off without a hitch, Napier says. The software automates the patching process and reduces the time it takes to distribute security fixes.
Managed from a single console, the technology provides real-time visibility and enforcement for all of the company’s endpoints, whether they are on or off the corporate network. Flexible, real-time reporting means that the bank is always prepared for an audit. Premier Financial also uses BigFix Lifecycle, which provides a full inventory of the bank’s software and hardware — another key report required by regulatory agencies.
Napier stresses that, along with researching available products, vendor support is the most important factor in choosing compliance and reporting technologies. It’s important to build a relationship with the vendor that will help the company meet current and future needs, he says.
“Spend all the time you need to compare the features of products and talk to others who have experience with the technologies,” Napier advises. “Find a vendor who is willing to partner with you and give the support you need now and later. Banking industry regulations change so rapidly that we’re always working hard to keep up.”
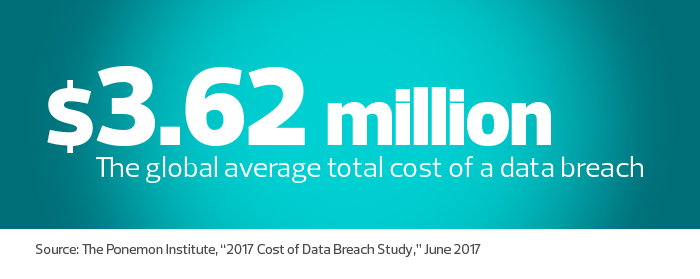
Compliance Is Easier than Suffering a Breach
Compliance and reporting can seem like a bureaucratic headache fraught with technical challenges, particularly in highly regulated New York state, but the alternative is a lot worse, says Ted Tomita, senior vice president and CTO of Catskill Hudson Bank.
“Compliance, especially related to security, is a tremendous focus for us, because we know that if we don’t do it right, we’ll end up on the front pages of newspapers,” says Tomita, whose bank is headquartered in Kingston, N.Y., with 16 locations in the Hudson Valley region. “It’s all about monitoring the network, knowing where your data is, managing patches and keeping the network safe. We are under constant threat from cyberattackers of all varieties.”
Catskill Hudson relies on layers of defense — anti-virus, intrusion detection, firewalls and more — with oversight from Tenable SecurityCenter, a platform that provides users with visibility, consolidated vulnerability and compliance management, as well as automated audit reports.

“SecurityCenter makes sure that all the programs we have in place to ensure compliance do what they’re supposed to do and provide the reports auditors look for,” Tomita says. “It gives us a view of how the security layers we have in place interact, and it validates the data from other systems.”
Robust reporting is critical, not only to satisfy state and federal auditors, but also for bank executives and the IT staff, he says.
“The bank is willing to spend money on products that make managing our security and compliance easier, but they like to see the results for themselves,” Tomita says. “I have to be able to relay actionable information that verifies compliance or supports spending decisions. And when reports alert us to potential vulnerabilities, IT doesn’t have to spend hours in front of a screen searching for them.”
While compliance strategies can be complex and ease of management is important, Tomita cautions against the temptation of simplicity when choosing tools. “Compromising security for simplicity is sheer stupidity,” he says. “Finding the right system to meet your needs might require adding resources or training, but it’s worth it.”
IDC’s Gelnaw adds that companies must understand the complexity of compliance and keep a comprehensive view of the effort in mind as they bring together technologies.
“You need to account for all your risks and reporting obligations and have tools to manage them,” she says. “Integration with other tools is imperative. Without it, you’ll never be able to see the complete compliance picture.”










