Review: Palo Alto Networks' PA-5020 Next-Gen Firewall Delivers Reliable, Targeted Security
Almost every small business, from the mom-and-pop shop on the corner to the 50-person design startup, now has some type of firewall. But as a business grows, the IT team eventually will need an enterprise tool, which is why Palo Alto Networks created its PA-5000 series of security appliances.
These next-generation firewalls have advanced features such as dedicated processing resources assigned to networking, security, signature matching and management functions — guaranteeing reliable and predictable ongoing performance. I took a look at the entry-level PA-5020 (though that hardly describes what this protection monster can accomplish).
The PA-5020 can handle large data streams. Designed for either general or specific deployments, such as guarding internet gateways, its maximum capacity is extremely high. At peak, it can process 120,000 new sessions per second — up to a maximum of 1 million. And if a business needs to go above that, it can swap out the PA-5020 for a PA-5050 (2 million maximum sessions) or PA-5060 (4 million).
Powerful Bandwidth Matched with Targeted Security
One of the secrets to the reliability of the PA-5020 is its built-in dedicated bandwidth. It has overall throughput of 5 gigabits per second, with 2Gbps dedicated to detecting threats and another 2Gbps to supporting virtual private network tunnels.
The applicance can support up to 2,000 simultaneous, monitored VPN tunnels without any negative impact on security — plus, up to 20 virtual routers.
When it comes to setting policies, the PA-5020 does a good job of giving administrators the ability to deploy granular security strategies. Using a Palo Alto next-gen firewall, a business can target policies at individual users, apps and content types, which makes it useful beyond security. The IT team can also perform peripheral security tasks, such as protecting bandwidth for critical apps.
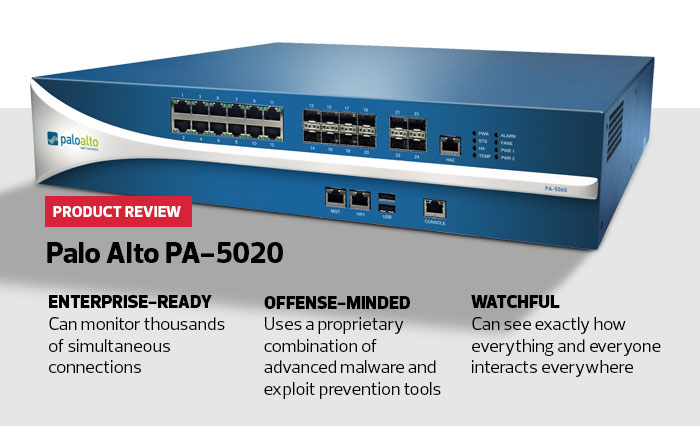
SPECIFICATIONS: Firewall Throughput 5Gbps, Threat Identification Throughput 2Gbps, Maxiumum Sessions Monitored 1 million, Maximum Number of Policies 10,000, Number of Supported Virtual Routers 20, Dimensions 16.5x17.5x3.5 inches, Weight 41 pounds
Less specific, blanket policymaking is also possible because it’s able to set policies across 80 security zones, each with its own set of enforced rules and permissions. In total, the PA-5020 can store and enforce up to 10,000 policies.
Businesses on a rapid growth path will want to consider investing in a security appliance like Palo Alto Networks’ PA-5020. Its easy-to-create and manage rules can help even a small IT team get a handle on security issues in the near term, while ensuring the business has a tool with the throughput to accommodate growth in the long term.
The Power of Segmentation
A subtle but powerful advantage of Palo Alto Network’s PA-5020 security appliance is that it is application-aware. Only advanced next-generation firewalls have that capability, which along with user and content types, can form a segmented security architecture not unlike the perimeter security approaches of old.
I tested the PA-5020 to determine if it would allow this type of precise control, which is a necessity for highly secure networks.
The PA-5020 enables clever systems administrators to define what is specifically allowed, especially within high-security zones, and create a blanket rule making everything else invalid. This is security by allowance, also called segmentation, instead of the more traditional firewall tactic designed around what can’t be done.
To test this, I created policies allowing the use of certain protocols tied to both specific users and applications. For example, I let one user on the test network use the FTP protocol as an interface between a defined web application and a database, which the user needed to do her job. I was able to set a policy that allowed this but did not give the user blanket FTP access. They could only use FTP as the interface between the specific app and database. I didn’t have to whitelist the entire protocol to do that.
Setting Security Parameters
After I set up several such allowance-based rules, I simply created a blanket policy that disallowed everything else. And presto, I had a narrowly defined segmented network that allowed the required work to be done, but denied everything else. Even in the event of a compromised credential, the hacker would still be restricted to a limited set of tasks, minimizing likely damage.
In terms of the real world, networks with thousands of users may not be suitable for this type of protection using the PA-5020. It would take too long to define thousands and thousands of such specific processes for users and content. Because the appliance offers up to 80 security zones, it makes sense to try segmentation within the highest security areas. There are fewer users and valid applications to configure, and doing so could really lock down those zones.
The PA-5020 can enable powerful segmentation in specific areas and enforce those rules without negatively impacting performance or throughput in other areas. Only an advanced next-generation firewall can support that level of segmentation, and the PA-5020 does so with relative ease.